Protecting your firm and your clients

Step 1: Take Stock
Know what personal information you have in your files and on your computers.
Button
Step 2: Scale Down
Keep only what you need for your business.
Button
Step 3: Lock It
Protect the information that you keep.
Button
Step 4: Pitch It
Properly dispose of what you no longer need.
Button
Step 5: Plan Ahead
Create a plan to respond to security incidents.
Button
Your Data Security & Privacy Toolkit
This Data Security & Privacy Toolkit from the National Association of REALTORS® aims to educate real estate professionals about the need for data security and privacy and to assist them in complying with legal responsibilities. Included are information on federal regulations regarding data security, checklists of issues to consider, sample policies created by the government and the FTC's "5 Key Principles to a Sound Data Security Program," which is highlighted here.
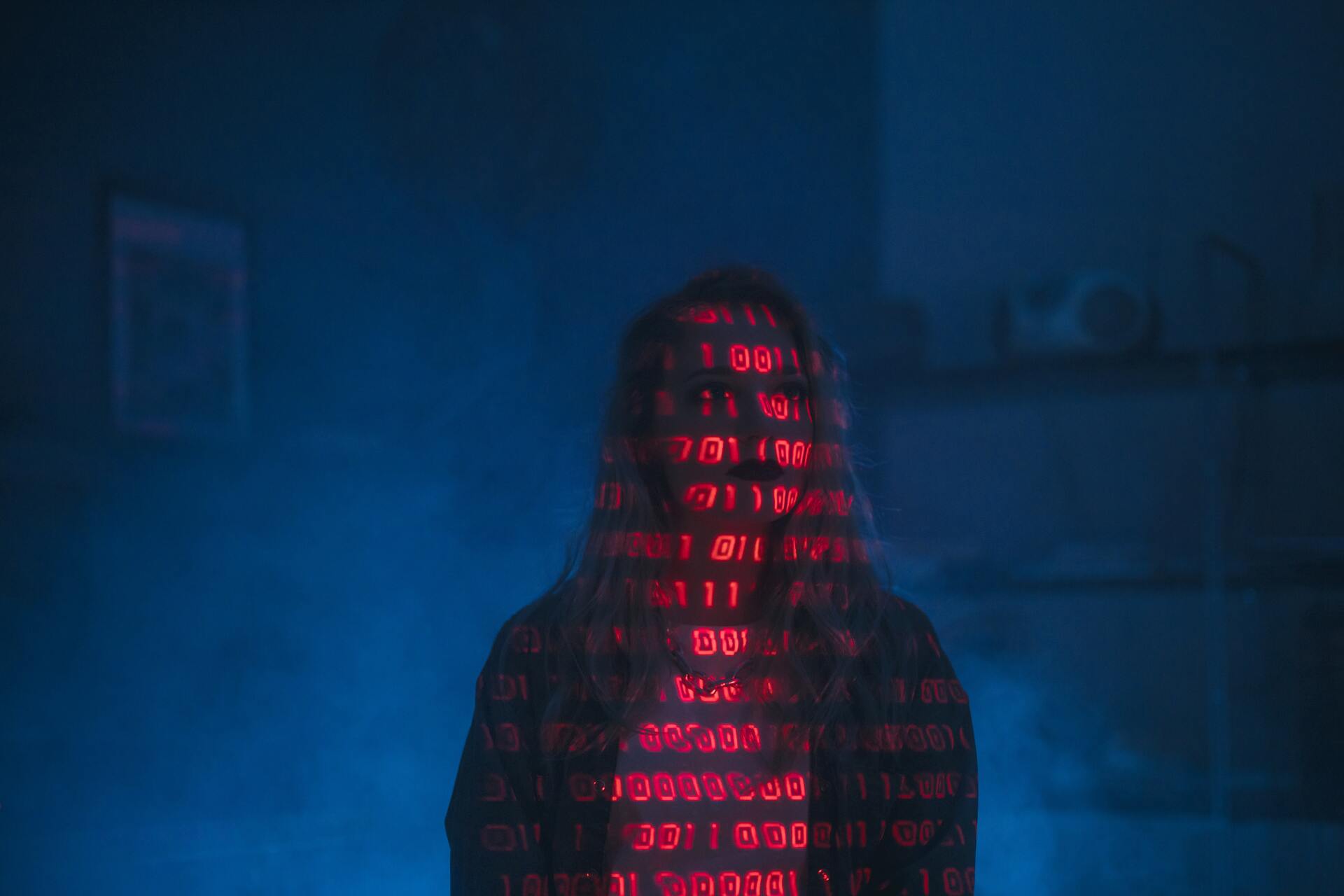
REALTOR® Cyber Security Resources
Cyber Security Checklist
for REALTORS®
Use these best practices to curb the risk of cybercrime in your everyday communications and transactions.
Preventing Cybercrime
During COVID-19
Use these tips to stay vigilant as you have been forced to adapt in an increasingly virtual world.
Wire Fraud Red Flags
To Watch Out For
One way to prevent wire fraud from affecting you is to familiarize yourself with common practices.
Wire Fraud Alert Form
for Clients
Have your clients sign a document that outlines the potential of wire fraud in real estate transactions.
Wire Fraud Email
Signature Notice
Add a notice about wire fraud into your email signature as a reminder to be on the lookout for anything suspicious.
Real Life REALTOR®
Wire Fraud Story
What started as an exciting home search ended in a cautionary tale for real estate professionals.
How to Report
Cases of Wire Fraud
The FBI stresses the importance of filing a report within 72 hours of the occurrence to attempt for best results.
Consider Cyber Insurance
through CyberPolicy®
Protect your business with a customized program created for REALTOR®-owned brokerages.
The information contained on this page and associated links are intended to provide Association members with general information regarding cyber security and wire fraud. The Association cannot warrant the accuracy of the information contained on this page and associated links as technology, law, and regulations are ever changing. The Association members are responsible for contacting their own attorneys and technology consultants for advice regarding how best to protect their offices and clients from cyber and/or wire fraud threats.
About Us
All rights reserved.
Useful Links
Contact Info
821 Main StreetBaton Rouge, LA 70802
Subscribe to Our Newsletter
Subscribe to newsletter
Thank you for subscribing to our newsletter.
Please try again later.